How the FBI took down Alphabay
by AKM
Posted on July 20, 2017 at 11:13 PM

2017 Best OPSEC Awards goes to Alphabay!
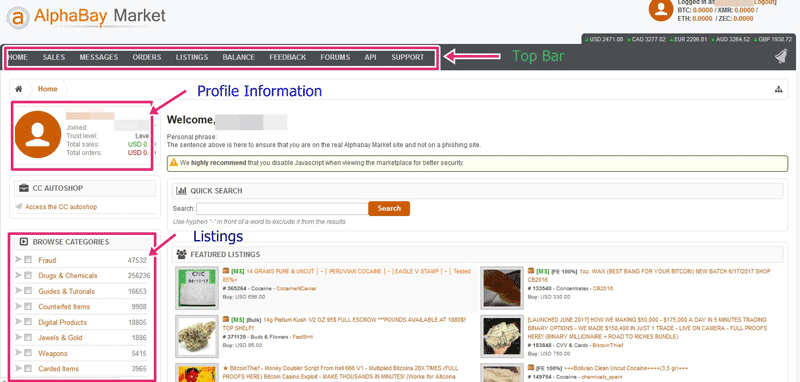
That’s the banner you’ll be presented with if you try visiting Alphabay at pwoah7foa6au2pul.onion. Alphabay, one of the darknet’s biggest marketplaces has been shutdown this month by the FBI alongside the DEA and Europol part of Operation Bayonet. Most people during this time are probably wondering where the Tor network 0day is. After all, isn’t that why the Tor devs recently opened a bug bounty program? To rat out all the exploits the feds are using? There isn’t one… yet. At least not that we know of. So how did Alphabay get shutdown? Almost the same way Silk Road got shut down, shit opsec.
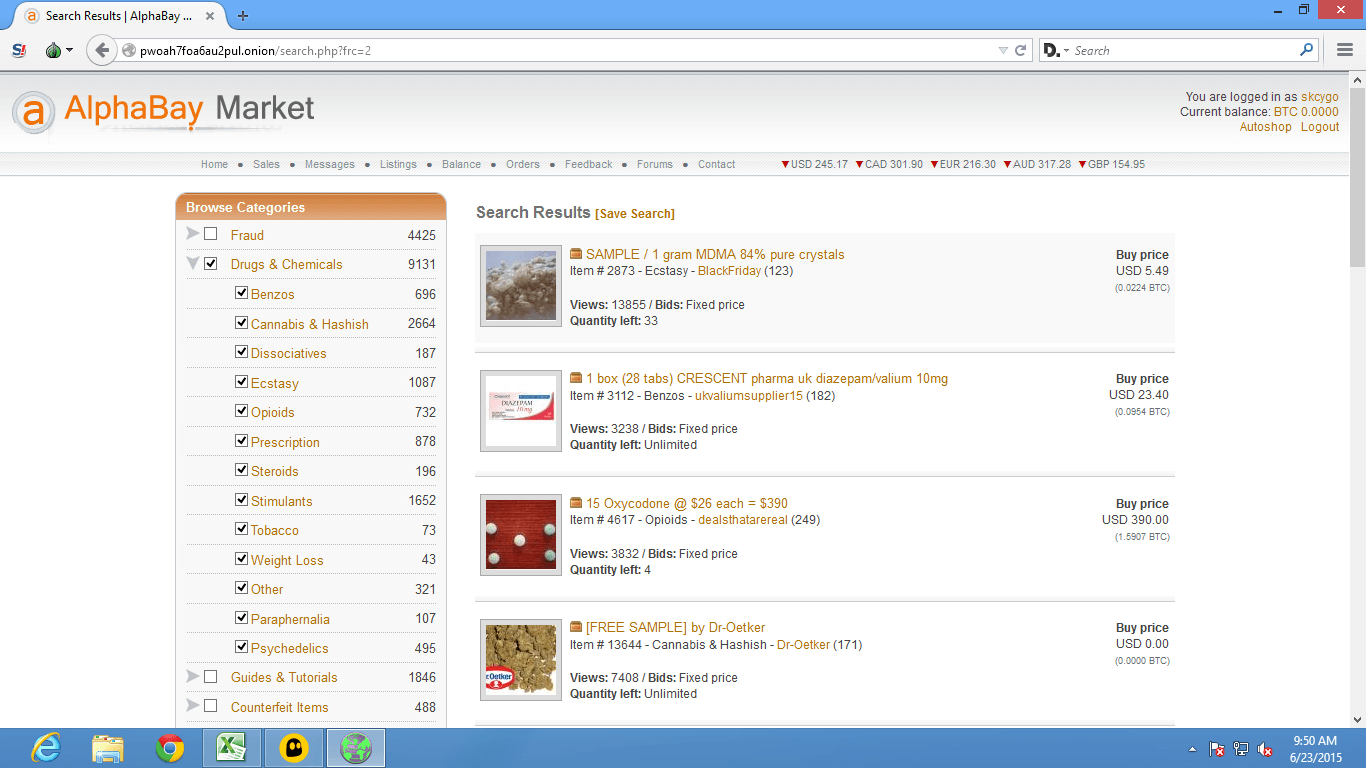
I’m going to get a little personal with this one, because it’s ridiculous. How could someone have the audacity to run a site that sells drugs, weapons, counterfeits, etc. and not secure their persona? Okay, what I’m about to tell you next will surely make you laugh. Alexandre Caze (the founder of Alphabay) was using a Hotmail account Pimp_Alex_91@hotmail.com to send out welcome and support emails from Alphabay! Yes you read that correctly, “Hey thanks for registering here at Alphabay, the world’s most notorious marketplace. If you need anything just email me here at my personal Hotmail”. This is exactly what caused Alphabay to get owned by the feds. Not some Tor network 0day.
On a side note, shout out to Troy Hunt for taking his time to build HaveIbeenPwned.com (a site dedicated to letting its visitors know how many data breaches they're compromised in) because what I’m about to show you next will seriously make you go bonkers. I did a little bit of investigative work with the Hotmail that Alexandre was using to send out welcome messages from Alphabay. Actually, to be completely honest, this required 0 effort. All I did was linger onto my curiosity and type in his Hotmail on HIBP just to see if it was linked to anything. And surely, it was. Not one, but FOUR different breaches were linked with his email account. Okay so what does this tell us? It tells us that Mr. Caze has a myspace, a 000webhost account (possibly to run tests before using it on the main site?), and a LinkedIn attached to his Hotmail account. That’s right. A notorious criminal’s Hotmail, happens to be linked to a personal LinkedIn account, sends welcome messages from Alphabay to its members. Okay, so maybe he wanted to brag about how much of a success Alphabay had become on his resume, big deal.
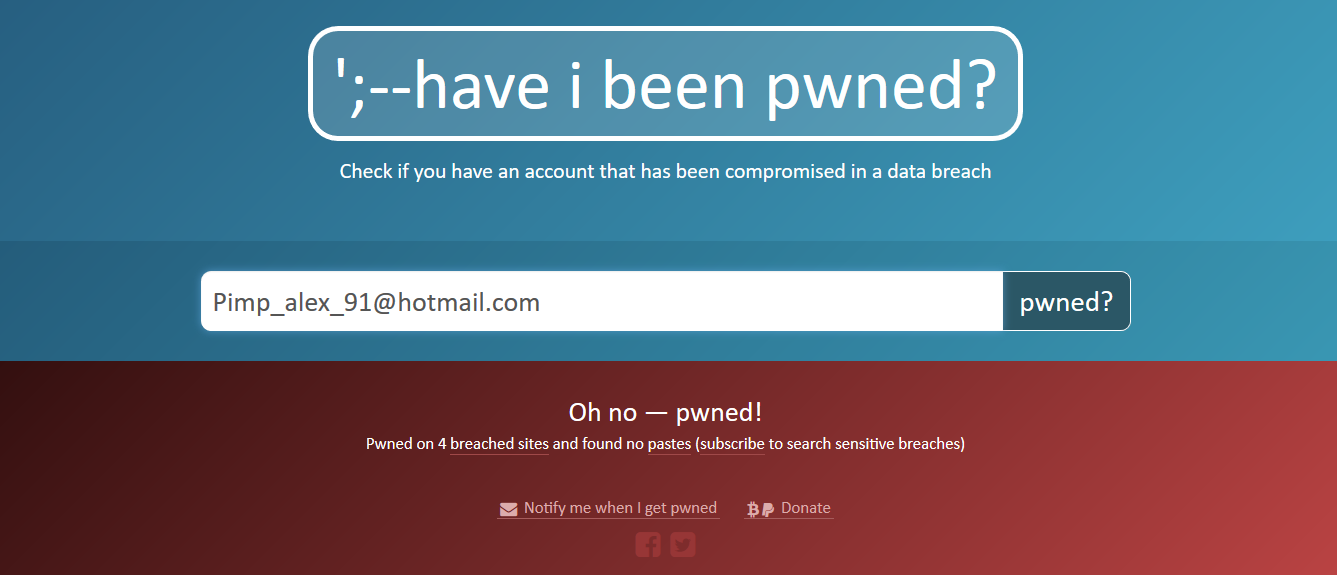
At this rate, the FBI doesn’t even need a warrant to ask Microsoft to hand over the details linked to that Hotmail, all they have to do is look through the old breaches! I’m surprised no one tried reusing the passwords supplied in those breaches to pwn Alphabay single-handedly. Or maybe Caze was smarter than that, used complex passwords to keep hosting, etc. away from getting breached into. If he can run such a site, surely, he has the skills to setup some sort of delivery automation from a different email? He could have at least used a different Hotmail (even though such criminals should never use such a platform when evading law enforcement). Silk Road faced a similar dilemma. For those who don’t know, Silk Road was another hidden site just like Alphabay that offered drugs, weapons, counterfeits, you name it. Ross Ulbricht (the founder of Silk Road) had used the handle “Dread Pirate Roberts” that of which had ties to his personal gmail, rossulbricht@gmail.com which he had posted online under a different handle asking about Silk Road. In both cases of Alphabay and Silk Road, there was no Tor 0day, just shit opsec.
Since we’re talking about Ross Ulbricht, might I also add to the fact that his gmail was found in 6 different breaches? I’m going to conclude this and give some genuinely good advice to any future drug infested marketplace on the Tor network; If you’re planning on running such sites, please for the love of god don’t reuse passwords, don’t reuse emails. And while you’re at it, stop abusing the Tor network for criminal activity, people genuinely use it for privacy reasons. This is how they all get pwned by the feds. Tor’s network will protect you to some degree but it will always be 99.999% human errors (server misconfigurations, or even using your private Hotmail to send out welcome messages) that brings these sites down. This advice should be followed by everyone to be fair, own your privacy, or it will own you.
InfoSec Related